top of page

THE ESSENTIALS
News, analysis and advice to support your digital transformation
![[Customer Case] 🚨 "Vincent, my website is selling medication... without my knowledge!"](https://static.wixstatic.com/media/dc9514_eb30f04ff0a2497c8ce3e18e4fc693e9~mv2.png/v1/fill/w_333,h_250,fp_0.50_0.50,q_35,blur_30,enc_avif,quality_auto/dc9514_eb30f04ff0a2497c8ce3e18e4fc693e9~mv2.webp)
![[Customer Case] 🚨 "Vincent, my website is selling medication... without my knowledge!"](https://static.wixstatic.com/media/dc9514_eb30f04ff0a2497c8ce3e18e4fc693e9~mv2.png/v1/fill/w_454,h_341,fp_0.50_0.50,q_95,enc_avif,quality_auto/dc9514_eb30f04ff0a2497c8ce3e18e4fc693e9~mv2.webp)
[Customer Case] 🚨 "Vincent, my website is selling medication... without my knowledge!"
This is a real-life case that I will detail during my next training session at the Community of Municipalities of the Cantilienne Area . Among many other cyber traps specifically targeting the leaders of very small and small businesses, we will see how to avoid this kind of catastrophic scenario. The story? An emergency call received less than a month ago from the manager of a premium tourist accommodation. With one click, his clients were being redirected to a foreign phar
May 111 min read
![[Technical Watch] Windows displays Secure Boot status: the end of the blind spot?](https://static.wixstatic.com/media/dc9514_1d634b64a2ca4f369289737a34b7a4a5~mv2.png/v1/fill/w_333,h_250,fp_0.50_0.50,q_35,blur_30,enc_avif,quality_auto/dc9514_1d634b64a2ca4f369289737a34b7a4a5~mv2.webp)
![[Technical Watch] Windows displays Secure Boot status: the end of the blind spot?](https://static.wixstatic.com/media/dc9514_1d634b64a2ca4f369289737a34b7a4a5~mv2.png/v1/fill/w_454,h_341,fp_0.50_0.50,q_95,enc_avif,quality_auto/dc9514_1d634b64a2ca4f369289737a34b7a4a5~mv2.webp)
[Technical Watch] Windows displays Secure Boot status: the end of the blind spot?
The latest Windows update now integrates the Secure Boot status directly into the settings. More than just an interface detail, it's a health indicator for your hardware chain of trust. The key issue: pre-boot integrity. Secure Boot is the only effective defense against rootkits and bootkits. These malware programs execute before the operating system, rendering your EDR/Antivirus solutions powerless because the kernel itself is already compromised. The operational observation
Apr 171 min read
![[Cyber-vigilance]: Anatomy of a #Smishing (SMS phishing) attempt](https://static.wixstatic.com/media/dc9514_a88c53cf91814a5680b75a3d02ed3cd2~mv2.png/v1/fill/w_333,h_250,fp_0.50_0.50,q_35,blur_30,enc_avif,quality_auto/dc9514_a88c53cf91814a5680b75a3d02ed3cd2~mv2.webp)
![[Cyber-vigilance]: Anatomy of a #Smishing (SMS phishing) attempt](https://static.wixstatic.com/media/dc9514_a88c53cf91814a5680b75a3d02ed3cd2~mv2.png/v1/fill/w_454,h_341,fp_0.50_0.50,q_95,enc_avif,quality_auto/dc9514_a88c53cf91814a5680b75a3d02ed3cd2~mv2.webp)
[Cyber-vigilance]: Anatomy of a #Smishing (SMS phishing) attempt
The scenario is well-rehearsed: I receive a #SMS "From the delivery driver" informing me that a package could not be delivered. A photo of a truck full of boxes was included to support this claim for credibility. 🪝 The catch? The SMS arrives at the exact moment I receive an Amazon delivery notification. My reflex: 1️⃣ Immediate suspicion 🫥: Never click on the link in the SMS. 2️⃣ Source verification: Opening the official Amazon app. 3️⃣ Proof by image: My packag
Mar 251 min read


⚠️ Security Alert: Your outdated iPhones are now hackable by anyone.
The BFMTV article confirms the release of Dark Sword, a tool that makes iOS hacking accessible without any technical expertise. The message is clear: update all your equipment (mobiles, servers and workstations) immediately. An unpatched endpoint is an open backdoor into your entire enterprise infrastructure. My approach: Faced with the democratization of these threats, my role as an external CIO is to structure your defense: 👉 Audit & Hygiene: Proactive identification of we
Mar 251 min read


"Is my system 100% secure?" This is the question every executive asks their CIO.
The answer is simple: "Are you 100% sure that you (or one of your colleagues) will never click on a fraudulent link?" Every day, 2 billion fraudulent emails are sent worldwide. Technology filters the vast majority, but zero risk does not exist. The attacker is no longer trying to force your reinforced door; he is waiting to be opened from the inside. Cybersecurity is not just a collection of software. It's a chain of vigilance where humans are the first line of defense... or
Mar 121 min read


1.2 million bank accounts compromised at Bercy. Monitoring your accounts is no longer enough.
The ZDNet article confirms a massive vulnerability in the FICOBA database. For an executive or CIO, the usual advice ("change your passwords") represents the bare minimum level of protection. Faced with the threat of SEPA direct debit fraud, we must move from a reactive mode to a total control mode. Here are my 3 priority recommendations for securing your company's cash flow: 1️⃣ The EBICS TS (Transport and Signature) protocol: This is the "standard" for banking security. Unl
Feb 231 min read


Supporting growth through shared expertise 🚀
This is precisely the ambition pursued by Frédéric LIOTARD , founder of 🟡 GROUPEACTIVE , which has been structuring this model for 30 years. Under the impetus of Frédéric Barbier , we continue to prove that access to high-level skills (Sales Management, HR, Purchasing, and of course IT) is the engine of resilience and innovation. As a member of 🟣 DSIACTIVE , my mission is clear: ✅ Secure your digital assets. ✅ Optimize your information systems. ✅ Manag
Jan 121 min read


Cisco is at the forefront of security against quantum cyber threats, but not immune to vulnerabilities.
Recent events perfectly illustrate this paradox. On the one hand, the deployment in Switzerland of a "quantum-safe" network with ID Quantique demonstrates that Cisco remains a cutting-edge technology leader. On the other hand, serious warnings about sophisticated cyberattacks serve as a reminder that even the best equipment has its vulnerabilities. 🔍 My feedback: Throughout my career as an IT Director, I have often chosen to limit the number of Cisco devices within our infra
Dec 22, 20251 min read

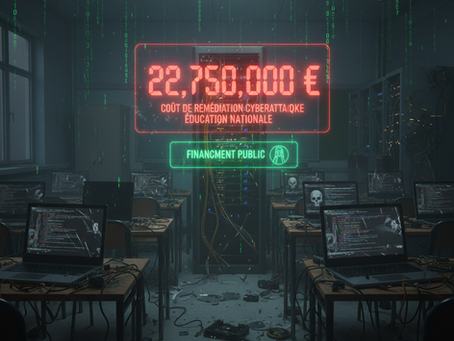
The cost of under-investing in cybersecurity – €22.75 million 💰💰💰
The cost of recovery from the cyberattack on high schools in Hauts-de-France: €22.75 million 💰💰💰 Let’s be clear: which private company could absorb such an expense just to get back on its feet? ❌❌❌ None ❌❌❌ Only “Enterprise France” survives, supported by public funds. For an SME or mid-sized company, €22.75M means certain bankruptcy. Investment in preventive cybersecurity is not a cost center. It is the only insurance policy that guarantees the continuity of your business.
Dec 12, 20251 min read


Cybersecurity Conference - 1 year later...
📍 Spring 2024, Chantilly Golf Course . Facing an audience of executives, I began my presentation on digital transformation with a shock tactic: 💥 330,000 successful cyberattacks in France in 2022. 7% of SMEs affected… but an average cost of €130,000 to recover. An already alarming figure, but this was only the tip of the iceberg. ⏩ One year later, in 2025, the situation had worsened: 💸 €466,000: average cost for a micro-enterprise/SME after an attack. 💼 €13 million
Sep 22, 20251 min read


An outsourced CIO who acts like a member of the team… and a trusted partner 🤝
When I get involved in a company, I don't stay on the sidelines. I sit down at the table, immerse myself in the culture, and act as if I were a full-fledged member of the team 🤝 Trust is at the heart of this approach. Because on a daily basis, I have access to what the company holds most sensitive: its data, its strategic projects, its vision. Without confidentiality and loyalty, it's impossible to build a strong and lasting collaboration 🔒✨ And this logic also extends to m
Sep 1, 20251 min read


GroupeActive and Microsoft reinvent sales proposals with Microsoft Copilot Studio
🟡 I'm proud to share this journey! At 🟡 GROUPEACTIVE and 🟣 DSIACTIVE we're truly committed to pushing boundaries with AI and Microsoft technologies. It's exciting to bring real innovation to the field—designed by and for independent professionals. Partnering with hashtag#MSPartner Witivio, we co-created GAIA Propale with Microsoft Copilot Studio. The result? A smart AI agent that helps our consultants write proposals 75% faster—directly inside Micro
Aug 1, 20251 min read


Microsoft admits: "I cannot guarantee that European 🇪🇺 data will never be transferred to the U.S. government 🇺🇸."
During a Senate hearing, Anton CARNIAUX, Legal Director of Microsoft France, acknowledged a reality often downplayed: the Cloud Act applies even to data hosted in European datacenters . 👉 If the parent company is American, U.S. law prevails . ⚖️ Why this matters:The Cloud Act allows U.S. authorities to request data held by any American provider, even if stored outside the United States . ✅ Practical solutions, even for SMEs: 🔹 Data Privacy Framework (DPF) (since 2023) gove
Jul 25, 20251 min read


Thank you to Parnasse for the invitation to the VivaTech 2025 trade show!
A dazzling edition, in every sense of the word — with spectacular immersive installations, humanoids that interact live, and robots on spherical wheels that captivate the crowds. 🌈🤖⚡️ 🧠 What I saw wasn't just technical demonstrators. It highlighted applied artificial intelligence, evolving robotics, and above all, their practical usefulness in our daily lives. What was a prototype five years ago is now a business solution. 🦊 Special mention to the orange robot with a fox
Jun 13, 20252 min read


🚀 Proud to share this wonderful recognition from Microsoft! 🚀
As an expert at 🟣 DSIACTIVE , a brand of 🟡 GROUPEACTIVE , it's a real pleasure to see our close collaboration with Microsoft highlighted in this official article. Thanks to optimized integration into hashtag#MicrosoftTeams , #GAIA (Groupe Active Intelligence Artificielle) leverages AI, and more specifically intelligent agents, to simplify prospecting work. This success demonstrates the digital expertise we bring to our work every day, and the impor
Jun 12, 20251 min read


🚨 Cybersecurity: Europe strengthens its digital sovereignty with the EUVD 🇪🇺
ENISA has launched the EUVD (European Vulnerability Database), a European database dedicated to vulnerabilities. This is an important step towards greater autonomy and responsiveness to cyber threats. 💬 My opinion: I'm following this type of development closely, especially for the systems installed at my clients' sites. Having an up-to-date European database allows me to be even more responsive in identifying and patching at-risk equipment. A real operational advantage. 🔍 A
Mar 30, 20251 min read


🔒 Protect your iPhone before it's too late! 📱
In our hyper-connected world, the security of our mobile devices is paramount. This carousel will guide you through the essential security settings for your iPhone and the crucial steps to take if your device is stolen. At 🟣 DSIACTIVE , we offer comprehensive solutions with enterprise mobile management (EMM) tools to ensure the security of your devices and data. Contact us to find out more! #MobileSecurity #iPhone #DSIActive #MobileManagement #EMM 🟡 GROUPEACTI
Sep 25, 20241 min read
bottom of page