top of page

THE ESSENTIALS
News, analysis and advice to support your digital transformation


Firewall and Stealth Mode on Mac: the two security settings you should enable right now
The ZDNet article reminds us of the importance of enabling the firewall and stealth mode on Macs. I've been doing that for a long time. What about you? In business, it's a constant balancing act between protection and agility: The Firewall (Blocking in the office): It filters incoming access. "Plug & Play" is a thing of the past; you must manually approve each new tool or network printer or risk being blocked. Stealth Mode (ideal for travel): It ignores diagnostic pings. A ha
May 171 min read
![[Customer Case] 🚨 "Vincent, my website is selling medication... without my knowledge!"](https://static.wixstatic.com/media/dc9514_eb30f04ff0a2497c8ce3e18e4fc693e9~mv2.png/v1/fill/w_333,h_250,fp_0.50_0.50,q_35,blur_30,enc_avif,quality_auto/dc9514_eb30f04ff0a2497c8ce3e18e4fc693e9~mv2.webp)
![[Customer Case] 🚨 "Vincent, my website is selling medication... without my knowledge!"](https://static.wixstatic.com/media/dc9514_eb30f04ff0a2497c8ce3e18e4fc693e9~mv2.png/v1/fill/w_454,h_341,fp_0.50_0.50,q_95,enc_avif,quality_auto/dc9514_eb30f04ff0a2497c8ce3e18e4fc693e9~mv2.webp)
[Customer Case] 🚨 "Vincent, my website is selling medication... without my knowledge!"
This is a real-life case that I will detail during my next training session at the Community of Municipalities of the Cantilienne Area . Among many other cyber traps specifically targeting the leaders of very small and small businesses, we will see how to avoid this kind of catastrophic scenario. The story? An emergency call received less than a month ago from the manager of a premium tourist accommodation. With one click, his clients were being redirected to a foreign phar
May 111 min read
![[Technical Watch] Windows displays Secure Boot status: the end of the blind spot?](https://static.wixstatic.com/media/dc9514_1d634b64a2ca4f369289737a34b7a4a5~mv2.png/v1/fill/w_333,h_250,fp_0.50_0.50,q_35,blur_30,enc_avif,quality_auto/dc9514_1d634b64a2ca4f369289737a34b7a4a5~mv2.webp)
![[Technical Watch] Windows displays Secure Boot status: the end of the blind spot?](https://static.wixstatic.com/media/dc9514_1d634b64a2ca4f369289737a34b7a4a5~mv2.png/v1/fill/w_454,h_341,fp_0.50_0.50,q_95,enc_avif,quality_auto/dc9514_1d634b64a2ca4f369289737a34b7a4a5~mv2.webp)
[Technical Watch] Windows displays Secure Boot status: the end of the blind spot?
The latest Windows update now integrates the Secure Boot status directly into the settings. More than just an interface detail, it's a health indicator for your hardware chain of trust. The key issue: pre-boot integrity. Secure Boot is the only effective defense against rootkits and bootkits. These malware programs execute before the operating system, rendering your EDR/Antivirus solutions powerless because the kernel itself is already compromised. The operational observation
Apr 171 min read
![[Technical Watch] 🔒 End of SharePoint and OneDrive OTPs for guests](https://static.wixstatic.com/media/dc9514_9d47a979fc9f428ea32a4c686f906ff4~mv2.jpg/v1/fill/w_333,h_250,fp_0.50_0.50,q_30,blur_30,enc_avif,quality_auto/dc9514_9d47a979fc9f428ea32a4c686f906ff4~mv2.webp)
![[Technical Watch] 🔒 End of SharePoint and OneDrive OTPs for guests](https://static.wixstatic.com/media/dc9514_9d47a979fc9f428ea32a4c686f906ff4~mv2.jpg/v1/fill/w_454,h_341,fp_0.50_0.50,q_90,enc_avif,quality_auto/dc9514_9d47a979fc9f428ea32a4c686f906ff4~mv2.webp)
[Technical Watch] 🔒 End of SharePoint and OneDrive OTPs for guests
Microsoft is gradually phasing out external shares based on OTPs (One-Time Passcodes). Specifically: ❌ Anonymous links will no longer work 👉 External users will need to be invited as guests in Entra ID (Azure AD B2B) ⚠️ The problem: many service providers haven't anticipated this change. The result? Your external sharing could stop overnight. ✅ Immediate audit of external access ✅ Migration to Entra B2B ✅ Application of security policies (MFA, Conditional Access) 💡 Strategi
Apr 11 min read
![[Cyber-vigilance]: Anatomy of a #Smishing (SMS phishing) attempt](https://static.wixstatic.com/media/dc9514_a88c53cf91814a5680b75a3d02ed3cd2~mv2.png/v1/fill/w_333,h_250,fp_0.50_0.50,q_35,blur_30,enc_avif,quality_auto/dc9514_a88c53cf91814a5680b75a3d02ed3cd2~mv2.webp)
![[Cyber-vigilance]: Anatomy of a #Smishing (SMS phishing) attempt](https://static.wixstatic.com/media/dc9514_a88c53cf91814a5680b75a3d02ed3cd2~mv2.png/v1/fill/w_454,h_341,fp_0.50_0.50,q_95,enc_avif,quality_auto/dc9514_a88c53cf91814a5680b75a3d02ed3cd2~mv2.webp)
[Cyber-vigilance]: Anatomy of a #Smishing (SMS phishing) attempt
The scenario is well-rehearsed: I receive a #SMS "From the delivery driver" informing me that a package could not be delivered. A photo of a truck full of boxes was included to support this claim for credibility. 🪝 The catch? The SMS arrives at the exact moment I receive an Amazon delivery notification. My reflex: 1️⃣ Immediate suspicion 🫥: Never click on the link in the SMS. 2️⃣ Source verification: Opening the official Amazon app. 3️⃣ Proof by image: My packag
Mar 251 min read


⚠️ Security Alert: Your outdated iPhones are now hackable by anyone.
The BFMTV article confirms the release of Dark Sword, a tool that makes iOS hacking accessible without any technical expertise. The message is clear: update all your equipment (mobiles, servers and workstations) immediately. An unpatched endpoint is an open backdoor into your entire enterprise infrastructure. My approach: Faced with the democratization of these threats, my role as an external CIO is to structure your defense: 👉 Audit & Hygiene: Proactive identification of we
Mar 251 min read
![[EVENT] Cybersecurity at the service of leaders in the Chantilly area 🛡️](https://static.wixstatic.com/media/dc9514_26380fdd44bb486488da0082a6b6c2e9~mv2.png/v1/fill/w_333,h_250,fp_0.50_0.50,q_35,blur_30,enc_avif,quality_auto/dc9514_26380fdd44bb486488da0082a6b6c2e9~mv2.webp)
![[EVENT] Cybersecurity at the service of leaders in the Chantilly area 🛡️](https://static.wixstatic.com/media/dc9514_26380fdd44bb486488da0082a6b6c2e9~mv2.png/v1/fill/w_454,h_341,fp_0.50_0.50,q_95,enc_avif,quality_auto/dc9514_26380fdd44bb486488da0082a6b6c2e9~mv2.webp)
[EVENT] Cybersecurity at the service of leaders in the Chantilly area 🛡️
Running a very small business or a small to medium-sized enterprise (SME) means constantly balancing priorities. However, digital security should no longer be a variable to be adjusted: it is the foundation of your business continuity. I am pleased to be leading a training session for executives, organized by the Community of Communes of the Cantilienne Area . The goal is clear: 0️⃣% jargon, 💯% operational. Together, we will address the critical points to protect your st
Mar 251 min read


"Is my system 100% secure?" This is the question every executive asks their CIO.
The answer is simple: "Are you 100% sure that you (or one of your colleagues) will never click on a fraudulent link?" Every day, 2 billion fraudulent emails are sent worldwide. Technology filters the vast majority, but zero risk does not exist. The attacker is no longer trying to force your reinforced door; he is waiting to be opened from the inside. Cybersecurity is not just a collection of software. It's a chain of vigilance where humans are the first line of defense... or
Mar 121 min read


1.2 million bank accounts compromised at Bercy. Monitoring your accounts is no longer enough.
The ZDNet article confirms a massive vulnerability in the FICOBA database. For an executive or CIO, the usual advice ("change your passwords") represents the bare minimum level of protection. Faced with the threat of SEPA direct debit fraud, we must move from a reactive mode to a total control mode. Here are my 3 priority recommendations for securing your company's cash flow: 1️⃣ The EBICS TS (Transport and Signature) protocol: This is the "standard" for banking security. Unl
Feb 231 min read


Cybersecurity for very small and small businesses: awareness is there. Now, it's time for action.
According to the latest study published by Cybermalveillance.gouv.fr : 📊 16% of very small and small businesses have suffered a cyberattack this year. 🔍 44% feel highly exposed. 🛡️ 58% believe they are well protected (+20 points in one year). 🔐 51% have a password policy. 📲 26% use two-factor authentication. 🚨 24% have a response plan. ⚠️ 80% do not feel truly ready to face it. Thanks to Cybermalveillance.gouv.fr for this useful and factual reminder. The figures are
Feb 171 min read


Outsourcing is often misunderstood.
It is associated with cost reduction, when it is primarily a matter of managerial clarity. In this intervention of Frédéric Barbier on BSMART 4Change , one point seems central to me: 👉 outsourcing is not delegating blindly, it is giving yourself the means to act faster and better, with immediately operational skills. In the field of very small and small businesses, I see it every week as an outsourced CIO at 🟣 DSIACTIVE : The leader rarely lacks vision. It mai
Jan 271 min read


The generalization of the MFA to the Ministry of the Interior is essential. But at this scale, this type of project inevitably takes a long time.
And that is precisely where the subject becomes strategic. When an MFA deployment takes months, or even longer, the real question is no longer just how to secure it today, but what that security will be worth at the end of the project. Attackers, however, don't wait. MFA fatigue, targeted phishing, session hijacking: MFA is no longer an end in itself. In such a critical ministry, the approach must be visionary: to think now about the post-MFA era — authentication without pass
Jan 201 min read


Supporting managers where the IT provider stops.
Too often, information systems are perceived as a cost center or a source of complexity. At Andiris , a member of the DSIACTIVE network , we are changing this view: your IT should be an engine of growth, not a hindrance. What is the difference? Unlike a service provider, an outsourced IT department integrates with your teams and acts exclusively in the interest of your strategy. We bring the rigor, absolute confidentiality and expertise necessary to secure your data and o
Jan 91 min read


🚀 New year, new identity for Andiris.
For 2026, Andiris is harmonizing its image. Today we are launching our new visual identity, which will now be featured across our entire website. This new logo reaffirms our three strategic pillars (the three yellow dots): 🟡 Innovate: Modernize your tools and practices. 🟡 Transform: Drive your IT towards performance. 🟡 Secure: Guarantee the integrity of your digital assets. A cosmetic evolution that reflects our requirement: clarity, rigor and operational efficiency. 👉 Di
Jan 81 min read


Cisco is at the forefront of security against quantum cyber threats, but not immune to vulnerabilities.
Recent events perfectly illustrate this paradox. On the one hand, the deployment in Switzerland of a "quantum-safe" network with ID Quantique demonstrates that Cisco remains a cutting-edge technology leader. On the other hand, serious warnings about sophisticated cyberattacks serve as a reminder that even the best equipment has its vulnerabilities. 🔍 My feedback: Throughout my career as an IT Director, I have often chosen to limit the number of Cisco devices within our infra
Dec 22, 20251 min read

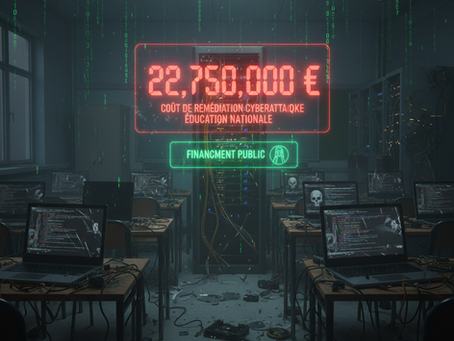
The cost of under-investing in cybersecurity – €22.75 million 💰💰💰
The cost of recovery from the cyberattack on high schools in Hauts-de-France: €22.75 million 💰💰💰 Let’s be clear: which private company could absorb such an expense just to get back on its feet? ❌❌❌ None ❌❌❌ Only “Enterprise France” survives, supported by public funds. For an SME or mid-sized company, €22.75M means certain bankruptcy. Investment in preventive cybersecurity is not a cost center. It is the only insurance policy that guarantees the continuity of your business.
Dec 12, 20251 min read


AWS & F5 - When giants falter
This week, two events that should give us pause for thought: ⚙️ Amazon Web Services (AWS) is experiencing a major outage in its US-East-1 region. As a result, services like Snapchat, Canva, or Capital.fr become partially or totally inaccessible. 🛡️ F5 Networks, a global cybersecurity company, has announced that it has been the victim of a sophisticated cyberattack. The intrusion is believed to be linked to a state-sponsored group. Internal data and source code have rep
Oct 23, 20252 min read


“Who has access to what in your company?”
This is a question I encounter very often in my work as an outsourced CIO. Behind it all, the same issues always lie: data security, regulatory compliance, and operational efficiency. I had the opportunity to share my experience in a white paper dedicated to access and password management. I offer a practical perspective: Why a centralized manager has become indispensable, and above all, what criteria should be considered to choose the right one in a business context. If this
Sep 30, 20251 min read


🚀 You've created your website using a CMS (🌐 WordPress, 🛠️ Wix, 🛍️ Shopify…) or an integrated CRM, and that's an excellent first step! 🎉
But did you know that ⚠️ 80% of security breaches and performance losses come from poor maintenance hygiene? Many leaders and entrepreneurs launch their website, then… ⏳ stop updating it. Result : ➡️ 💀 Hacking risks ➡️ 🐢 Degraded user experience (outdated plugins, slowness, bugs 🐞) ➡️ 👻 Loss of visibility (SEO penalized by Google if the site is not optimized 🔍) ➡️ 😬 Unprofessional image (outdated design = lack of credibility 🎨) Here is the essential checklist for
Sep 28, 20251 min read


Apple security alert – urgent update
A zero-day vulnerability is currently being exploited on iOS, iPadOS, and macOS. It could allow attackers to compromise your devices and data. Update all your Apple devices immediately: 👉iOS 18.6.2 / iPadOS 18.6.2 👉 macOS Sequoia 15.6.1, Sonoma 14.7.8, Ventura 13.7.8 Access paths for the update: 👉 iPhone / iPad: Settings → General → Software Update 👉 Mac: Apple menu → System Preferences → Software Update For companies with mass deployment tools, now is the ideal time to u
Sep 25, 20251 min read
bottom of page